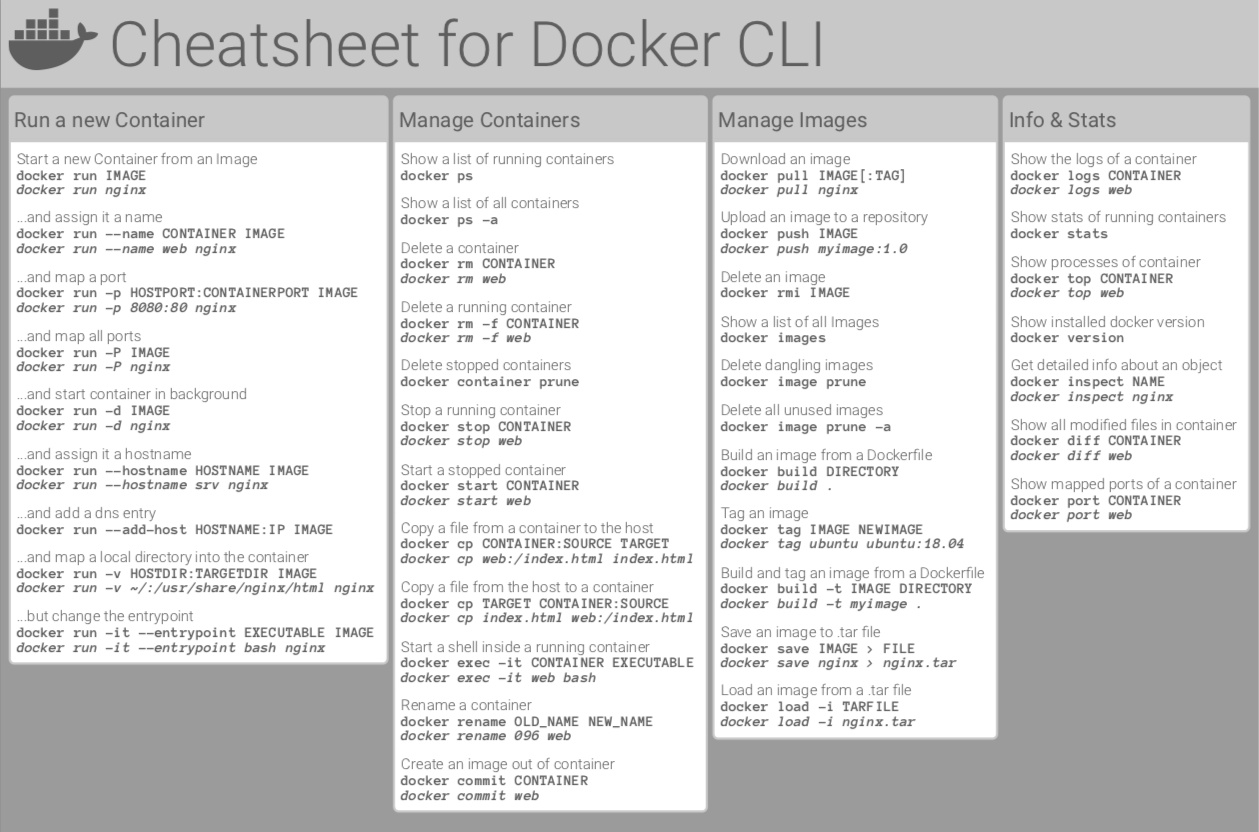
Docker Cli Cheat Sheet
The Ultimate Docker Cheat Sheet Docker - Beginners Intermediate Advanced View on GitHub Join Slack The Ultimate Docker Cheat Sheet. Complete Docker CLI. Container Management CLIs. Inspecting The Container. Interacting with Container. Image Management Commands. Image Transfer Comnands. Builder Main Commands. Awscli AWS CLI chef Chef circle CircleCI deis Deis docker-compose docker-compose docker Docker CLI dockerfile. Cask-index Caskroom index cheatsheet-styles Cheatsheet styles commandline Command line stuff cordova Apache Cordova datetime Date & time formats devise Devise divshot Divshot figlet Figlet firebase Firebase firefox Firefox freenode. Common use Docker CLI commands. Contribute to alesandrog/DockerCheatSheet development by creating an account on GitHub. Docker Cheat Sheet Run Build Manage Images and Containers Images List all images Remove images Containers Start existing container Stop running container List running containers List all containers Remove containers Logs.
Estimated reading time: 13 minutes
Looking to speed up your development cycles? Quickly detect and learn how to remediate CVEs in your images by running docker scan IMAGE_NAME. Check out How to scan images for details.
Vulnerability scanning for Docker local images allows developers and development teams to review the security state of the container images and take actions to fix issues identified during the scan, resulting in more secure deployments. Docker Scan runs on Snyk engine, providing users with visibility into the security posture of their local Dockerfiles and local images.
Users trigger vulnerability scans through the CLI, and use the CLI to view the scan results. The scan results contain a list of Common Vulnerabilities and Exposures (CVEs), the sources, such as OS packages and libraries, versions in which they were introduced, and a recommended fixed version (if available) to remediate the CVEs discovered.
For information about the system requirements to run vulnerability scanning, see Prerequisites.
This page contains information about the docker scan CLI command. For information about automatically scanning Docker images through Docker Hub, see Hub Vulnerability Scanning.
How to scan images
The docker scan command allows you to scan existing Docker images using the image name or ID. For example, run the following command to scan the hello-world image:
Get a detailed scan report
You can get a detailed scan report about a Docker image by providing the Dockerfile used to create the image. The syntax is docker scan --file PATH_TO_DOCKERFILE DOCKER_IMAGE.
For example, if you apply the option to the docker-scan test image, it displays the following result:
Excluding the base image
When using docker scan with the --file flag, you can also add the --exclude-base tag. This excludes the base image (specified in the Dockerfile using the FROM directive) vulnerabilities from your report. For example:
Viewing the JSON output
You can also display the scan result as a JSON output by adding the --json flag to the command. For example:
In addition to the --json flag, you can also use the --group-issues flag to display a vulnerability only once in the scan report:
You can find all the sources of the vulnerability in the from section.
Checking the dependency tree
To view the dependency tree of your image, use the --dependency-tree flag. This displays all the dependencies before the scan result. For example:
For more information about the vulnerability data, see Docker Vulnerability Scanning CLI Cheat Sheet.
Limiting the level of vulnerabilities displayed
Docker scan allows you to choose the level of vulnerabilities displayed in your scan report using the --severity flag.You can set the severity flag to low, medium, or high depending on the level of vulnerabilities you’d like to see in your report.
For example, if you set the severity level as medium, the scan report displays all vulnerabilities that are classified as medium and high.
Provider authentication
If you have an existing Snyk account, you can directly use your Snyk API token:
If you use the --login flag without any token, you will be redirected to the Snyk website to login.
Prerequisites
To run vulnerability scanning on your Docker images, you must meet the following requirements:
Download and install Docker Desktop Edge version 2.3.6.0 or later.
Sign into Docker Hub.
From the Docker Desktop menu, select Sign in/ Create Docker ID. Alternatively, open a terminal and run the command
docker login.(Optional) You can create a Snyk account for scans, or use the additional monthly free scans provided by Snyk with your Docker Hub account.
Check your installation by running docker scan --version, it should print the current version of docker scan and the Snyk engine version. For example:
Note:
Docker Scan uses the Snyk binary installed in your environment by default. If this is not available, it uses the Snyk binary embedded in Docker Desktop.The minimum version required for Snyk is 1.385.0.
Supported options
The high-level docker scan command scans local images using the image name or the image ID. It supports the following options:
| Option | Description |
|---|---|
--accept-license | Accept the license agreement of the third-party scanning provider |
--dependency-tree | Display the dependency tree of the image along with scan results |
--exclude-base | Exclude the base image during scanning. This option requires the --file option to be set |
-f, --file string | Specify the location of the Dockerfile associated with the image. This option displays a detailed scan result |
--json | Display the result of the scan in JSON format |
--login | Log into Snyk using an optional token (using the flag --token), or by using a web-based token |
--reject-license | Reject the license agreement of the third-party scanning provider |
--severity string | Only report vulnerabilities of provided level or higher (low, medium, high) |
--token string | Use the authentication token to log into the third-party scanning provider |
--version | Display the Docker Scan plugin version |
Known issues
WSL 2
- The Vulnerability scanning feature doesn’t work with Alpine distributions.
- If you are using Debian and OpenSUSE distributions, the login process only works with the
--tokenflag, you won’t be redirected to the Snyk website for authentication.
Feedback
Your feedback is very important to us. Let us know your feedback by creating an issue in the scan-cli-plugin GitHub repository.
Docker, scan, Snyk, images, local, CVE, vulnerability, securityIn this tutorial, I have written some command for docker CLI cheat sheet. Docker the essential for DevOps Roles.
The build image from our Dockerfile.
Docker run a command in an image
Docker Cli Cheat Sheet Download
Manage containers
Docker Create a container from an image.
Example, Create and start a container
Exec Run commands in a container.
Example, Docker ssh container
Start and stop a container.
Manage containers using ps and kill.
Docker Images
Manages images.
Deletes images.
Conclusion
Docker Cli Cheat Sheet Printable

Thought the article, You can use “Docker CLI cheat sheet“ as above. I hope will this your helpful.
